Protecting your online privacy and security has become crucial, especially as we primarily rely on the internet for many parts of our lives. As netizens, we must make proactive efforts to safeguard ourselves. The digital world is rife with potential hazards, such as identity theft and data breaches. In this blog article, we’ll delve into valuable tips and techniques that will enable you to strengthen your digital security. Also, you will learn how to guarantee your online privacy and security.
Understanding the Importance of Online Privacy and Security
The Value of Online Privacy and Security
Internet privacy is the legal right to decide what information is shared and to keep our private information safe from unwanted access. We can preserve our independence, secure critical data, and keep our identities hidden.
The Significance of Online Privacy and Security
Internet security focuses on defending our digital assets, gadgets, and data against online dangers. These dangers include hacking, malware, and phishing scams. It guarantees the privacy, reliability, and accessibility of our online identity.

Various Ways Hackers Break Digital Security
Many types of digital security breaches can occur. Therefore, it’s critical to be aware of them to protect oneself. The following are some typical techniques used by hackers to compromise security:
- Phishing Attacks: To fool you into disclosing personal information like passwords or credit card numbers, hackers send phoney emails or messages that appear to be real.
- Malware Infections: Viral or ransomware-type malicious software can infect your computer through downloads, hacked websites, infected emails, or infected downloads.
- Social Engineering: Hackers use social engineering to influence individuals by impersonating people they know and trust. With this, they coerce them into disclosing private information or get them to take actions that jeopardise security.
- Brute force attacks: If your password is weak or simple to guess, hackers will attempt a large number of username and password combinations before they locate the one that works.
- Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS): Attacks called Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) occur when hackers overload a network or website with traffic to the point where it is inaccessible to authorised users.
- SQL Injection: Hackers take advantage of holes in websites to access databases without authorization and steal or modify data.
- Man-in-the-Middle (MitM) Attacks: Attacks called “Man-in-the-Middle” (MitM) include hackers interfering with two parties’ communications and changing them to stealthily gather sensitive data.
- Zero-day Exploits: To obtain unauthorised access or control, hackers target unpatched, undiscovered vulnerabilities in software or systems.
- Insider Threats: Insider threats occur when employees of a company erroneously use their access privileges to damage security.
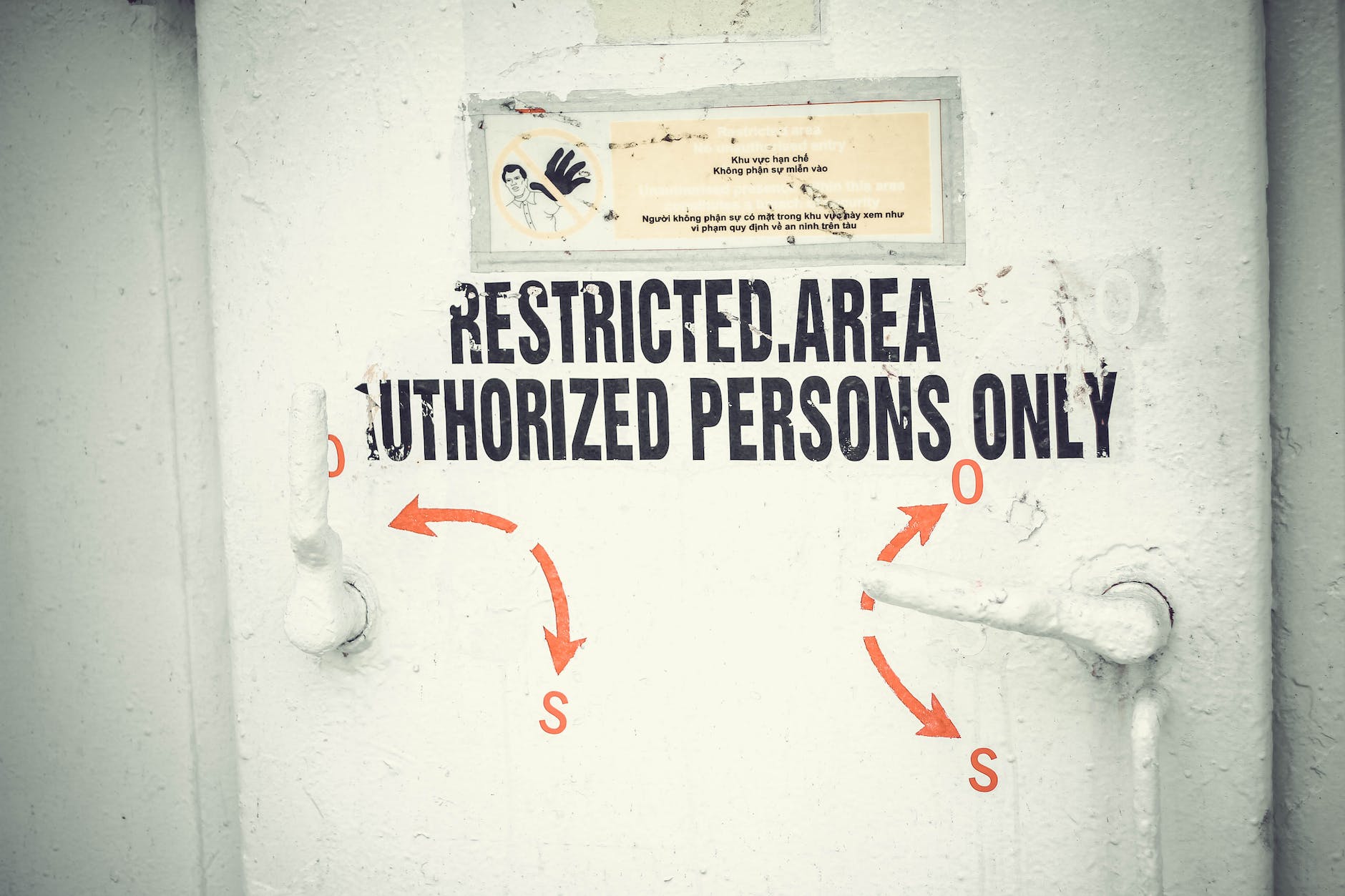
- Physical Security Breaches: Physical security breaches occur when hackers physically access systems or devices, such as by stealing gear or breaking into restricted regions.
Practical Steps to Enhance Online Privacy and Security
You may take precautions to protect yourself by being aware of these techniques. Use strong passwords, update your software, and be aware of who has access to your devices and systems. It’s crucial to keep up with developments and take precautions to strengthen your online safety.
Strong Passwords and Two-Factor Authentication
For each online account, start by using secure, one-of-a-kind passwords. Use a mix of symbols, numerals, and capital and lowercase characters. When feasible, enable two-factor authentication (2FA), which increases security by requiring an additional verification step.
Upgrade your devices’ software.
To make sure you have the most recent security updates, you should often upgrade your operating system, programmes, and hardware. Keeping things up-to-date is essential because outdated software may have flaws that hackers might exploit.
Use personal information with caution.
When revealing personal information online, use caution. Be careful about how much personal information you provide to websites and online services. Keep your social media data usage to a minimum. Examine privacy options to limit what others can see.
Secure Your Internet Connection
While viewing sensitive information or engaging in online transactions, be sure your internet connection is safe and encrypted. Never do private business on a public Wi-Fi network. Use virtual private networks (VPNs) to add an additional layer of encryption. In doing this, you will be shielding your online activity from prying eyes.
Adopt safe browsing habits
When online, use caution. Avoid downloading files from dubious sources, clicking on questionable links, or opening attachments from shady senders. To find and stop malware attacks, use dependable antivirus software and keep it updated.
Regularly Back Up Your Data
Periodically backup your critical information to a cloud storage platform or an external hard drive. Having a backup assures that you won’t lose important information in the event of a security breach or device malfunction.
Use caution while dealing with social engineering and email attacks.
Avoid phishing emails and other social engineering schemes that try to get you to divulge private information. Never send critical information by email or other insecure means. Always confirm the legitimacy of requests before sending any information, and be wary of unwanted communications.
Examine and modify the privacy settings
Review and modify the privacy settings on your social media platforms, applications, and internet accounts frequently. Limit the information that is accessible to others and choose the maximum level of privacy.
Learn and keep yourself informed.
Keep up with the most recent privacy laws, cybersecurity best practices, and new dangers. To keep abreast of emerging threats and effective defences, follow respected cybersecurity blogs and news sources, and sign up for industry newsletters.
Pay Attention to Online Transactions
Before doing online transactions, make sure the website is safe by checking the URL for HTTPS and the padlock icon in the address bar of your browser. Don’t divulge financial or credit card information on unsafe websites.
You may put up a strong barrier around your online presence by carrying out these useful strategies and taking a proactive approach. You can maximise the advantages of living in a connected world. At the same time, you can also lower the dangers by protecting your online privacy and security. This will not only provide you with peace of mind. Conquer the digital world with confidence by taking control of your digital life and fortifying your online castle.
Till I come your way again, don’t forget to subscribe to Doyin’s Honest Notes and enjoy a drop of honey for your day…
[…] caution while sharing sensitive personal information on social media networks. Examine and modify your privacy settings to limit who has access to your information. Avoid oversharing, and think about the ramifications […]